Control D and NextDNS
For years I have successfully subscribed to the service NextDNS. This has opened my eyes to what goes on in my network when accessing the internet.
Access to the internet was in the early days largely available at the universities. Tools like e-mail, ftp, telnet and gopher were used as means to communicate on for instance DEC VAX/VMS-terminals. Around 1993 the web browser Mosaic made it’s debut, and it was available on the SUN Sparc-station which had a stunning graphical interface.
It may be hard to grasp what a game-changer this was. Moving internet interaction from purely text based to a full blown graphical interface made it into a more pleasant experience.
Image downloaded from http://www.forbes.com/sites/jonathansalembaskin/2015/04/17/is-opera-the-browser-innovation-wild-card/
Using hyperlinks made navigation between pages more fluent and intuitive. You could easily visit different sites simply by clicking on an indexed word with your mouse.
Eventually internet became more available at home by using a dial-up modem. One issue with the increased connectivity is that there is a lot of data circulating between users and servers. This data could easily be captured on the network using a packet sniffer.
A packet is a unit that is sent between a sender and a listener on the internet. The traffic is separated into smaller units at the sender side, called packets. These packets are assembled back at the receiver.
“Big data”-analysis would not to be introduced for several years so it was still a huge undertaking tracking user activities. As time went on the tools got more advanced and computing power increased. The ability to eavesdrop increased.
With the transition from http to https the content is eventually encrypted and the ability to listen to the traffic decreased. Now it’s up to the service providers what they store. This is why it’s a recommended reading the privacy policy on the pages you visit. This is a daunting task but luckily there are organizations interpreting this, for instance https://tosdr.org/en.
This shifted the importance from network sniffing to capture DNS-requests. DNS is short for Domain Name System and it’s purpose is to translate the Unified Resource Locator (URL) entered in the browser to the address of the service requested. A web page is visited by specifying a specific URL-string.
For instance, when visiting https://en.wikipedia.org it finds the address the owner has reported to a domain registry. The domain registry is a list of all domains and it’s corresponding address.
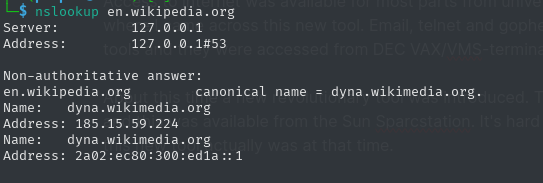
nslookup is used to lookup domains.
In this example, en.wikipedia.org has an ip v4-address of 185.15.59.224. This is used by the web browser when connecting to a port on that machine. Without the address the browser cannot establish a connection. The procedure to lookup an address is called resolving.
Normally the internet provider is the default resolver. This means the provider can track all the visited domains and potentially store this information indefinitely or pass it on to other parties. Other resolvers are Google and Quad 9.
Instead of using the default DNS resolver, there are custom ones like NextDNS and Control D.
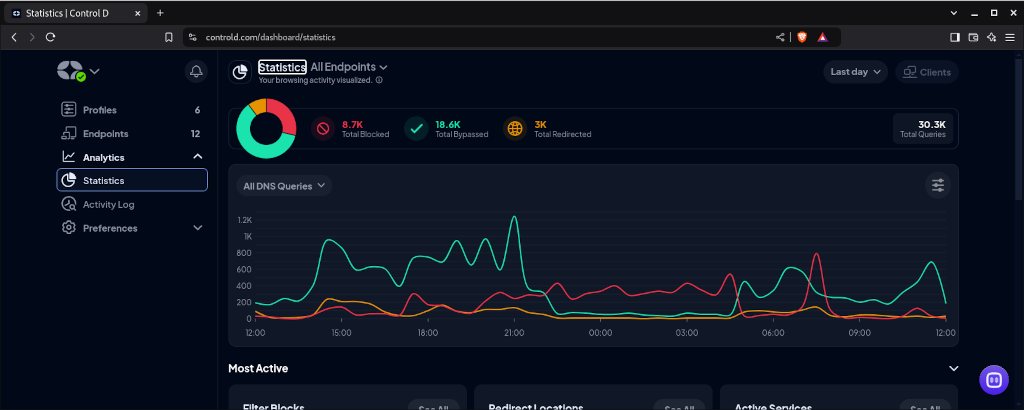
All DNS lookups will be stored in the cloud for these custom services. This allows the account owner access to logs that can be analysed in real-time. It also enables blocking of domains.
To the browser a blocked domain appears as if the service is not reachable and results in an “404 Page not found”-error.
This opens up three use cases:
- To deny minors access to age-restricted content
- To lock down all internet activities at specific times
- To block access to fraudulent pages
There is a fourth bonus case which enables blacklisting of all domains. In order to access a resource it has to be white-listed. Only pages that has been allowed can be visited. This is time consuming but it will open up a deeper understanding of the activities in the network. Invalid or malicious calls will be blocked.
 Image downloaded from https://www.palmtech.net/2018/09/04/art-invisibility-kevin-d-mitnick/
Image downloaded from https://www.palmtech.net/2018/09/04/art-invisibility-kevin-d-mitnick/
In Kevin Mitnicks’ book “The Art of Invisibility” the importance of separating sensitive accounts from each other is outlined. Banking is performed on a dedicated device for this, and accessing social media is restricted to another. By also implementing a custom DNS all interactions from the applications to the internet are restricted.
Having experience from using both NextDNS and Control D, they are both very capable and have similar features. To get the most out of them they require a bit of tinkering and testing. Initially use the basic profiles.
If custom DNS is a new concept to you, Control D and NextDNS are excellent starting points.